How Access Is Controlled by Tokens
Access control via tokens enforces what a requester may do, where, and under which conditions. Tokens…
Access control via tokens enforces what a requester may do, where, and under which conditions. Tokens…

Monolithic architectures unify code, data, and deployment in a single, cohesive unit. Microservices split systems into…

Monetizing digital content requires a balanced mix of audience reach, product fit, and price sensitivity. Data…
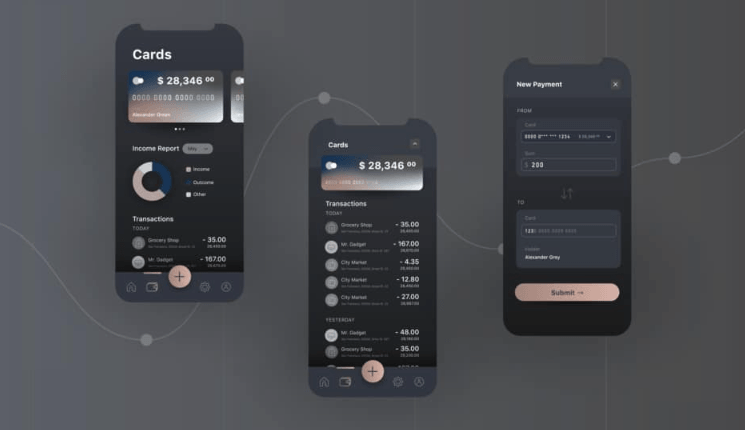
Mobile UX design is shifting toward faster, lean interfaces that respect small screens. Users expect instant…
End of content
End of content